ISMS – information security guideline of our organisation

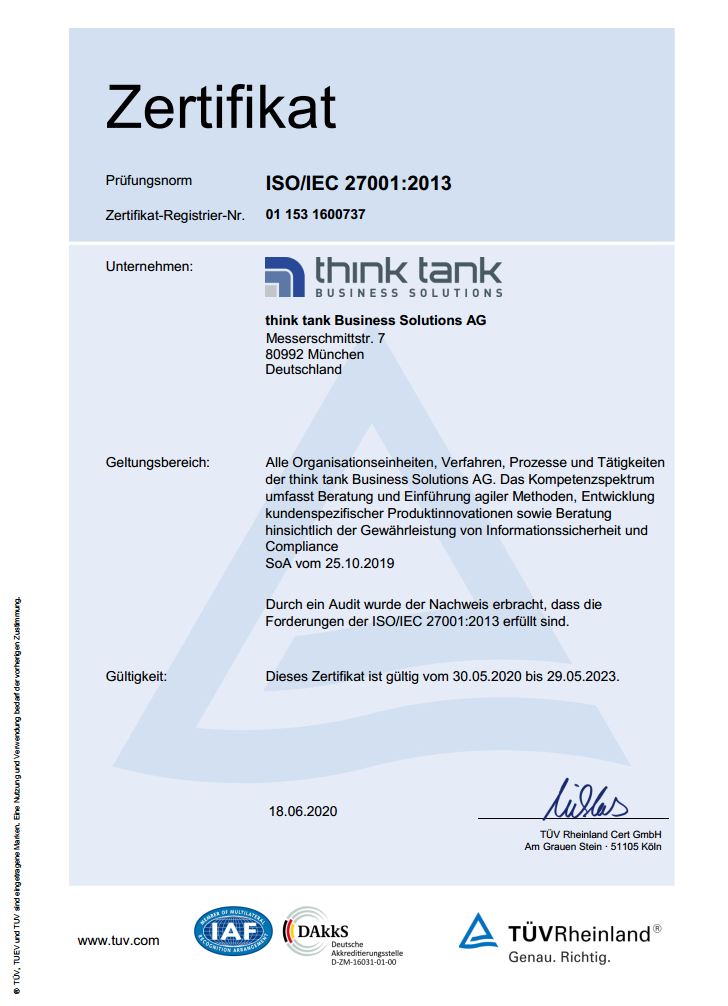
Certified in accordance with ISO 27001:2013
We, think tank Business Solutions AG, Messerschmittstraße 7, 80992 Munich (hereinafter: think tank) have implemented an Information Security Management System (ISMS) according to ISO 27001:2013. The ISMS is intended to form the basis for systematically identifying and managing existing risks. The ISMS also has the function of ensuring the continuous improvement of the protection goals for information security – confidentiality, integrity, availability. The think tank’s ISMS applies to all organisational units. It therefore includes all procedures, processes and activities of the company. If third parties are commissioned with the provision of services, contractual agreements must ensure that the information security guideline is taken into account in the service relationships.
Scope of the ISMS according to ISO27001:2013
The Board of Directors is responsible for the information security of think tank. As part of this responsibility, the Executive Board issues this information security guideline. According to this guideline, each area of think tank is responsible for the security and appropriate protection of information. These measures are not only required by law, but are also part of our obligations towards our customers. Every employee must therefore adhere to this guideline and the standards derived from it.
Target group
These guidelines are binding for all employees of think tank. All employees are requested by the Executive Board to actively implement information security on the basis of this guideline and in accordance with ISO 27001, data protection in accordance with the BDSG and EU-DSGVO and material security to the best of their ability in their respective areas of activity.
Responsibilities
In addition to the Executive Board as the overall responsible party, all those involved in the business processes are also responsible for information security. The Executive Board actively supports the measures and strategies of information security and promotes the implementation of security measures in the company. Each person responsible has to pay particular attention to the following in his or her area:
- Assessing and determining the business relevance of the information and data for which he or she is responsible,
- determining and approving the scope of security and controls to adequately ensure the availability, confidentiality and integrity of the information and data for which he or she is responsible,
- ensuring that responsibilities are explicitly defined and security and control measures are implemented to manage and protect the information and data for which he or she is responsible,
- ensuring that the systems used to process the information and data for which he/she is responsible are regularly audited for compliance with the Information Security Policy.
All employees are required to comply with the guideline and any derived guidelines when creating, using and managing information and data. Employees are responsible for all actions they take when using information and related systems. Employees must understand that information security is central to the company’s philosophy and develop appropriate security awareness. Employees who suspect or become aware of a breach of information security and related information security standards, or who suspect that information is not appropriately protected, must report it immediately to their supervisor and/or the Information Security Officer. Non-compliance or deliberate violation of company requirements may result in disciplinary action, dismissal and criminal and/or civil proceedings, depending on their extent.
Security awareness
Due to the importance of information security, every employee is expected to maintain a high level of security awareness. Their compliance will be monitored. Security awareness is characterised by the following behaviour:
Recognising that information security is a critical and essential element of the company’s philosophy and success,
constant security awareness in all daily activities,
personal accountability for proactive as well as effective reactive measures in relation to all risks, vulnerabilities, incidents to employees, information, assets and the continuation of business in the event of an emergency,
the Information Security Officer is informed immediately of any irregularities.
Goals
As the importance of information security is central to the execution of business processes, the following key, strategic information security objectives emerge:
Protection of confidential data of both customers and the company and its employees,
Availability of all services and thus the availability of the data involved,
Integrity of all services and thus the integrity of the data involved,
– Preservation of the value invested in technology, information, work processes and knowledge,
Compliance with the requirements resulting from legal, contractual and regulatory obligations,
Ensuring the continuity of work processes within the company,
Establishing and maintaining a good reputation of the company with regard to information security in the public awareness,
Reducing the costs incurred in the event of a loss.
Minimum or need-to-know principle: Access to security-critical systems, applications and information must be restricted to a minimum number of people. In principle, what is not explicitly permitted is prohibited (prohibition with reservation of permission).
Introduction and ongoing maintenance of the ISMS based on the idea of continuous improvement in the sense of the PDCA model (Plan-Do-Check-Act).
Provision of sufficient resources to achieve the set goals.
Risk management
Risk management is the basis of the ISMS according to ISO 27001. The risk analysis within the framework of the ISMS serves to systematically consider potential risks, followed by their evaluation and, if necessary, the initiation of countermeasures. The risks existing for information technology and security are recorded and evaluated according to a given scheme. The application of appropriate, economic measures, the shifting of business risks and the lowering or conscious acceptance of risks below a defined, acceptable level are described in the risk analysis and countersigned by the Executive Board.
Continuous improvement process
The ISMS based on the PDCA model is implemented to maintain and continuously improve information security. Improvement measures from various sources flow into the PDCA cycle, and their implementation is continuously documented.